Cyber deception is the most effective way to identify threat actors in any organization’s network. Read on for insight into how it works to deliver actionable threat intelligence across industries.
Highlights.
-
In a recent interview with David Brown, the driving force behind strategic alignment at our organization, and CounterCraft partner Bosch CyberCompare, we delved into the latest advances in threat intelligence solutions, focusing on the power of deception technology to deliver specific, actionable intel in real-time. With a wealth of experience in international sales management across… Read more

-
Detected in the Wild – How We Identified A Real Threat Actor Exploiting an Unpatched Fortinet Product Read more

-
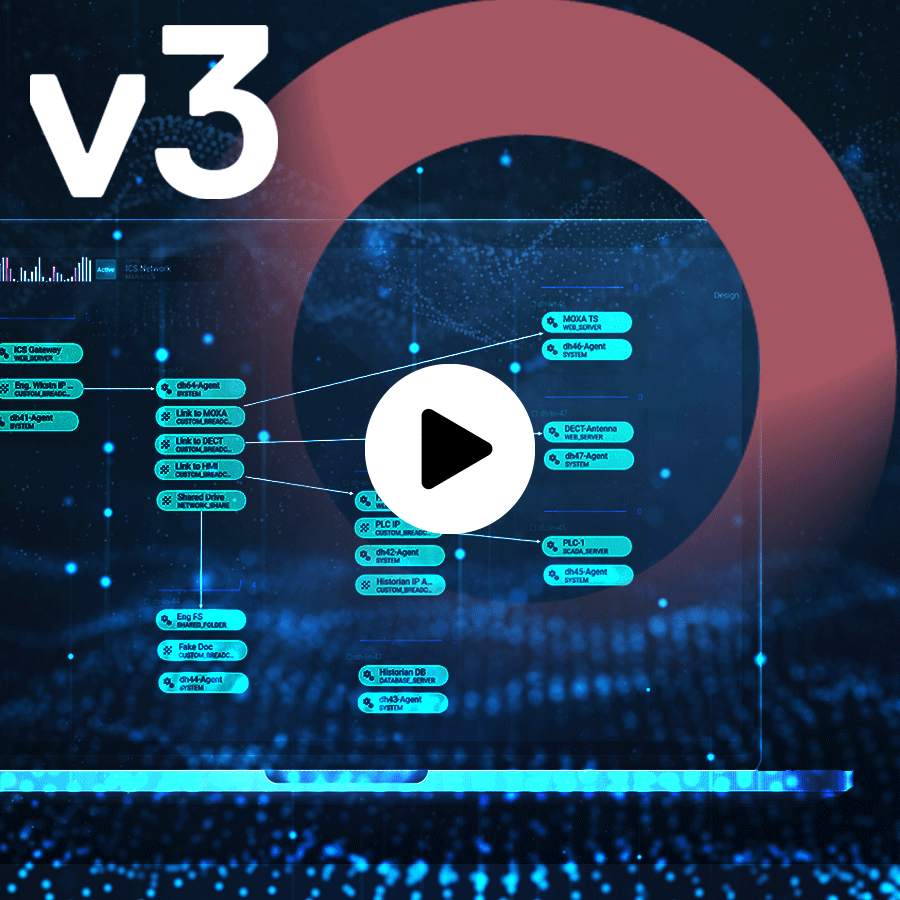
CounterCraft’s Version 3.4 release of The Platform™ introduces several key new features to improve the threat intelligence delivered by our powerful deception technology. Read more

-
Categories: Company News
As we reflect on the year 2023, we are incredibly proud of the progress we have made as a company and the positive impact we have had on our customers’ security posture. We have faced many challenges along the way, but our team has demonstrated resilience, innovation, and an unwavering commitment to delivering a cutting-edge… Read more

-
Since the start of the Internet, honeypots have been a very valuable defensive strategy. No matter how simple or complex they are, they definitely add a lot of value to your security posture. Clifford Stoll and his marvelous book The Cuckoo’s Egg is always referenced as one of the first deception use cases in cybersecurity,… Read more

-
Find Out How CounterCraft Delivers Actionable Adversary-Generated Threat Intelligence Read more

-
ICS security is challenging. See how Red Electrica used deception technology to prevent attacks on their OT systems. Read more